Bear Security – Security News for the Week of July 19th, 2021

These are the stories that relate to our careers, clients, and businesses in the cybersecurity world for the Week of July 19th, 2021. This week’s edition is blog-only so that I can focus on my studies for my CEH exam later this week. We will resume our full distribution next week. Thanks for understanding!
REvil Ransomware Group Goes MIA
The Register is reporting that the websites run by the ransomware group REvil have gone offline weeks after their massive exploitation of Kaseya’s VSA software that impacted more than 1,500 businesses. So far, no details have come out as to whether this was intentionally done by the group, or if this was the result of political or law enforcement action.
The shutdown also impacts anyone who was intending to pay the ransom, as the systems to pay it have also gone offline.
Read the full story over on The Register.
SolarWinds Serv-U Product Vulnerable with Exploit in the Wild
BleepingComputer is reporting that a vulnerability in SolarWinds Serv-U products are actively being exploited in the wild. So far, the exploitation seems to be sourced from a single threat actor performing targeted attacks according to Microsoft Security researchers.
The vulnerability affects Serv-U managed File Transfer Server and Serv-U Secured FTP, and if exploited, allows an attacker to run arbitrary code with privileges. Solarwinds has released patches to address the vulnerability which you can access in the SolarWinds customer portal.
Read the full story over on BleepingComputer or review the SolarWinds Security Advisory.
SonicWall SRA & SMA Devices at Risk of Ransomware
SonicWall published an urgent security advisory for customers of their Secure Mobile Access (SMA) 100 series and Secure Remote Access (SRA) products that are running unpatched or EOL 8.x firmware. Devices running this firmware are currently being targeted in a ransomware campaign through the use of stolen credentials.
Any devices that cannot be upgraded to the 9.x firmware or higher, should be shut down and decommissioned as they cannot be protected from the vulnerability. SonicWall also recommends that all credentials in their SMA or SRA devices should be reset, along with having multifactor authentication enabled.
Read the full security advisory over at SonicWall.
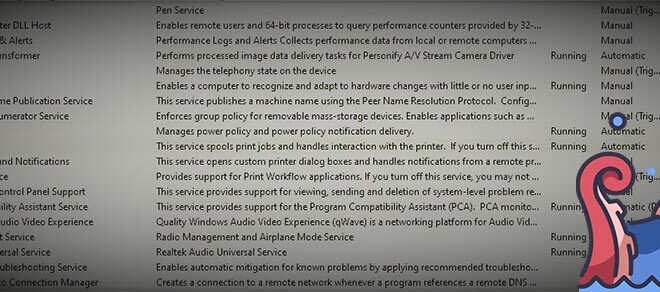
Another Print Spooler Vulnerability in Windows
If you were hoping we were in the clear on print spooler, we aren’t. TheHackerNews and others are reporting that Microsoft has shared fresh, limited guidance on another vulnerability in the print spooler. The new vulnerability is being tracked as CVE-2021-34481, and is a local privilege escalation flaw that can be used by an attacker to run code with SYSTEM level privileges. Unlike the other three vulnerabilities reported in recent weeks, this one can only be exploited locally, requiring a valid user account.
Microsoft’s current guidance as of writing is to disable the print spooler to be protected while they work on a patch. As this guidance is unrealistic for critical systems, we recommend you disable the print spooler (as a rule) on any system where printing isn’t required, and set the appropriate keys mentioned in our earlier coverage to block remote print access if the printers don’t need to be shared. Further, we encourage you to stay vigilant and monitor for unusual behavior on systems where the print spooler must be functional.
Read the full story over on TheHackerNews or the security advisory from Microsoft.
Colorado Joins Virginia and California in Passing a Consumer Privacy Law
SC Magazine is reporting that Colorado has become the third U.S. state to pass a comprehensive consumer privacy law, which takes effect in 2023. Consumer privacy has been a major issue for years as consumers recognize how companies have been using and abusing their data. While it’s good that more States are seeing the importance of such laws, a growing patchwork of laws with different rules and guidelines will complicate businesses that operate nationwide.
It’ll be interesting to see how they turn out over time. Will most States pass very similar laws, will they be all over the place, or will Congress finally do something? Only time will tell.
Read the full story over at SC Magazine.
Things Not Mentioned
- Microsoft and Citizen Lab identify zero-day‘s used by Israeli Spyware Vendor, Candiru.
- Kryptos Logic posts updates they found in Trickbot and Zeus.
That’s all for this week’s security news. Come back every Monday morning for the next rendition or check it out over on YouTube or on podcast. Stay safe out there friends.