Bear Security – Security News for Week of May 29th, 2021
These are the stories that relate to our careers, clients, and businesses in the cybersecurity world for the Week of May 29th, 2021. Watch this in video form over on YouTube, or you can listen on the go with the Bear Security podcast.
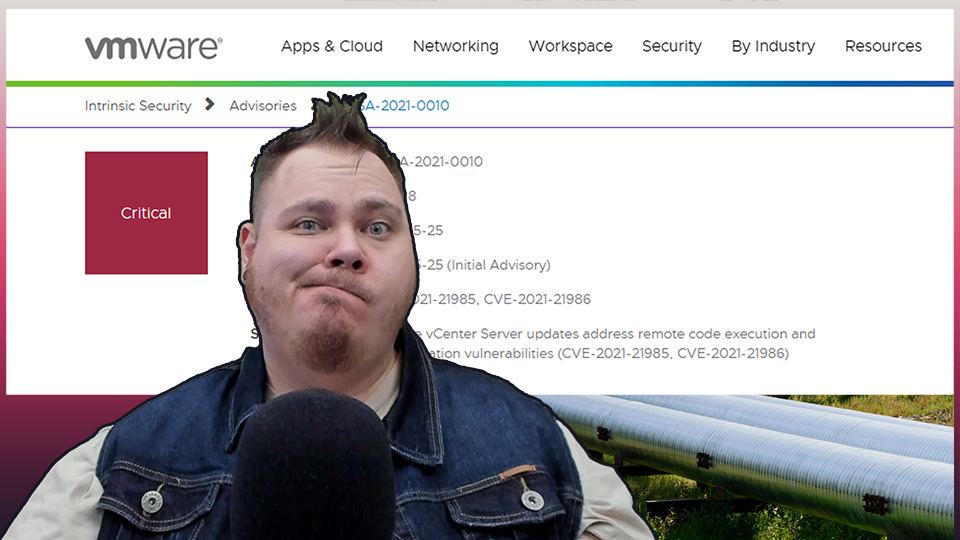
VMWare Releases Another Major Patch for vCenter
On Tuesday, ARS Technica reported that VMware disclosed and patched a severe vulnerability that resides in VMWare vCenter Server with a CVSS severity score of 9.8. The Remote Code Execution vulnerability exists in the HTML5 vSphere client due to a lack of input validation in the Virtual SAN Health Check plug-in, which is enabled by default. So, a malicious actor with network access to port 443 could exploit this to execute commands without restrictions on the underlying OS that hosts the vCenter server. VMWare vCenter versions 6.5, 6.7, and 7.0 are all affected.
This is the second VMWare vCenter vulnerability this year carrying such a high CVSS score. The first came out back in February that was also a Remote Code Execution vulnerability that stemmed from a lack of authentication in the vRealize Operations plugin. Within a day of VMWare announcing this initial vulnerability, proof-of-concept exploits appeared from at least 6 different sources. So, you don’t want to hesitate in patching this.
Read the full story over on ARS Technica, or view the VMWare Advisory. You can review an RCE PoC from the February vulnerability from researcher straightblast.
Apple Users Urged to Update, Again
It seems not much time has gone by recently since we’ve announced several urgent rounds of updates that applied to Apple products as of late. Gizmodo is reporting that on Monday, Apple released iOS version 14.6 that addresses more than 40 security issues that affect iPhone, iPad, and iPod Touch. These updates run the gamut with exploits ranging from malicious audio files that allow remote code execution, to granting full control or even revealing personal information. Users are urged to update immediately.
If you’re using macOS, you aren’t missing out on updates either. In addition to the iOS updates on Monday, TechCrunch is reporting that Apple also released a patch for a third zero-day that allows malicious code to essentially piggyback off legitimate apps permissions and inherit them, thereby allowing the malware to avoid getting flagged. While this allows for an attacker to take screenshots of the user’s desktop, researchers for Jamf believe the bug could also be used to access a victim’s microphone, webcam, or capture keystrokes of a user. These findings come off continued research being done of the XCSSET malware, which was uncovered just over a month ago that was exploiting multiple zero-day vulnerabilities to bypass macOS security defenses without anything standing in its way.
View the full iOS Story over at Gizmodo, or on the macOS zero-day over at TechCrunch. You can also check out the Apple Advisories for iOS or for macOS. Lastly, you can read up on the research performed by Jamf regarding the XCSSET Zero-Day TCC bypass over on their blog.
Feds Move to Regulate Critical Infrastructure Security
SC Magazine is reporting that on Wednesday the Department of Homeland Security and the Transportation Safety Administration has put in place new mandatory cybersecurity requirements around oil and natural gas pipelines. The order is the first of its kind as the government works to understand and prevent what happened with Colonial Pipeline earlier in the month from happening to other operators.
The order mandates that pipeline operators alert the Cybersecurity and Infrastructure Security Agency of all cybersecurity incidents, to install a designated and always available coordinator to handle any problems, and they must audit systems within 30 days to ensure they are in line with cybersecurity guidelines that had not previously been mandated or enforced.
Read the full story over at SC Magazine.
Microsoft’s Threat Intelligence Center Discusses Ongoing Email Attacks from NOBELIUM
Microsoft’s Threat Intelligence Center (MSTIC) published a blog on Thursday regarding new sophisticated email-based attacks from threat actor NOBELIUM. The threat actor was behind the attacks against SolarWinds, the SUNBURST backdoor, TEARDROP malware, GoldMax malware, and others. Microsoft has been tracking the ongoing evolutions of this email-based attack campaign by the group since January 2021. On May 25th, the threat actor leveraged the commercial mass-mailing service, Constant Contact, masquerading themselves as a US-Based development organization like USAID to distribute malicious URLs to a wide target base.
The current evolution seeks to compromise systems through a spear-phishing campaign that leverages an HTML file attachment. Once the attachment is opened by the user, it would activate JavaScript within the file that then writes an ISO to the user’s computer. It then encourages the user to open it which would mount the file. From there, a shortcut file would execute an accompanying DLL file, which would result in a Cobalt Strike Beacon executing on the user’s system, and additional payloads may arrive from there.
While Microsoft believes automated systems blocked emails to the more than 3,000 individual accounts across more than 150 organizations that NOBELIUM was targeting, those that got through could have resulted in some successful executions.
View the full details, sample emails, defensive guidance, and Indicators of Compromise over on the MSTIC blog.
Windows HTTP Vulnerability Affects WinRM on Servers and Windows 10
This is an update from our coverage regarding the May Patch Tuesday updates. This past patch Tuesday introduced a fix for a wormable HTTP exploitation in Windows. Well, turns out according to Bleeping Computer, this doesn’t just affect Windows IIS servers. This can also be used to attack unpatched Windows 10 and Server systems that have exposed the Windows Remote Management (WinRM) service. The scope of the WinRM vulnerability applies to versions 2004 and 20H2 of Windows 10 and Windows Server. So if you haven’t installed this month’s patches, its probably a good idea to get on it now.
Read more over on Bleeping Computer.
Retailer Mercari Joins the List of Those Impacted by CodeCov Breach
Mercari issued a press release last Saturday that confirmed that malicious actors were able to access a part of their source code and gain access to a limited set of personal information because of the CodeCov breach. Data that was accessed was limited to proceeds information from dates in 2013 and 2014, some customer service records from Nov 2015 and 2018, along with records related to business partners and employees.
Mercari joins at least 4 other organizations that have confirmed breaches related to CodeCov with more expected. Read the full press release which outlines the full extent, and their investigation related to how it affected them, over on their website.
Could Future Computer Processors Thwart Hackers Through Augmentation
Could Microprocessors of the future use augmentation to thwart attempts of hackers? That’s the topic of a research brief published by The Conversation Thursday before last, about a secure new computer processor dubbed Morpheus. Morpheus is part of a DARPA-funded program known as SSITH or Systems Security Integrated Through Hardware and firmware, that seeks to break the cycle of vulnerability exploitation against hardware architectures by addressing their underlying weaknesses.
This microprocessor thwarts hackers by randomly changing its underlying infrastructure. 525 security researchers spent three months last summer trying to hack the processor and have so far failed. Researchers working on Morpheus at the University of Michigan say that while a skilled hacker could reverse-engineer a Morpheus machine in as little as a few hours if given the chance, they counter this by having the chip change its microarchitecture every few hundred milliseconds.
While the technology continues to be refined and researched, it’s interesting to see what could be on the horizon to further secure the hardware that powers our world.
Read the research brief over on The Conversation or a more in-depth breakdown over at IEEE Spectrum.
Things Not Included in This Week’s Episode
- The National Institute for Standards and Technology (NIST)’s comment period for HIPAA implementation guidance is open through June 15th.
- Shannon Morse‘s concerns regarding Walt Disney World testing facial recognition. (P.S. also check out her show ThreatWire!)
- SysInternals was updated!
- SC Magazine’s Story on how Security Pros rely on Peer Groups and Open Communication to help with stress.
- Freenode IRC may have been taken over by Korea’s “crown prince”.
That’s all for this week’s security news. Come back every Saturday for the next rendition or check it out over on YouTube or on podcast. Have a good week (and holiday weekend) everyone!